What Is Social Engineering? How Attackers Hack People, Not Computers (2026)
Someone clicks a link in an email that looks like it came from their bank. Within minutes, their account is drained. No malware was needed. No code was exploited. The only thing that got hacked was the person's trust. This is what social engineering looks like in practice, and it's far more common than most people realize.
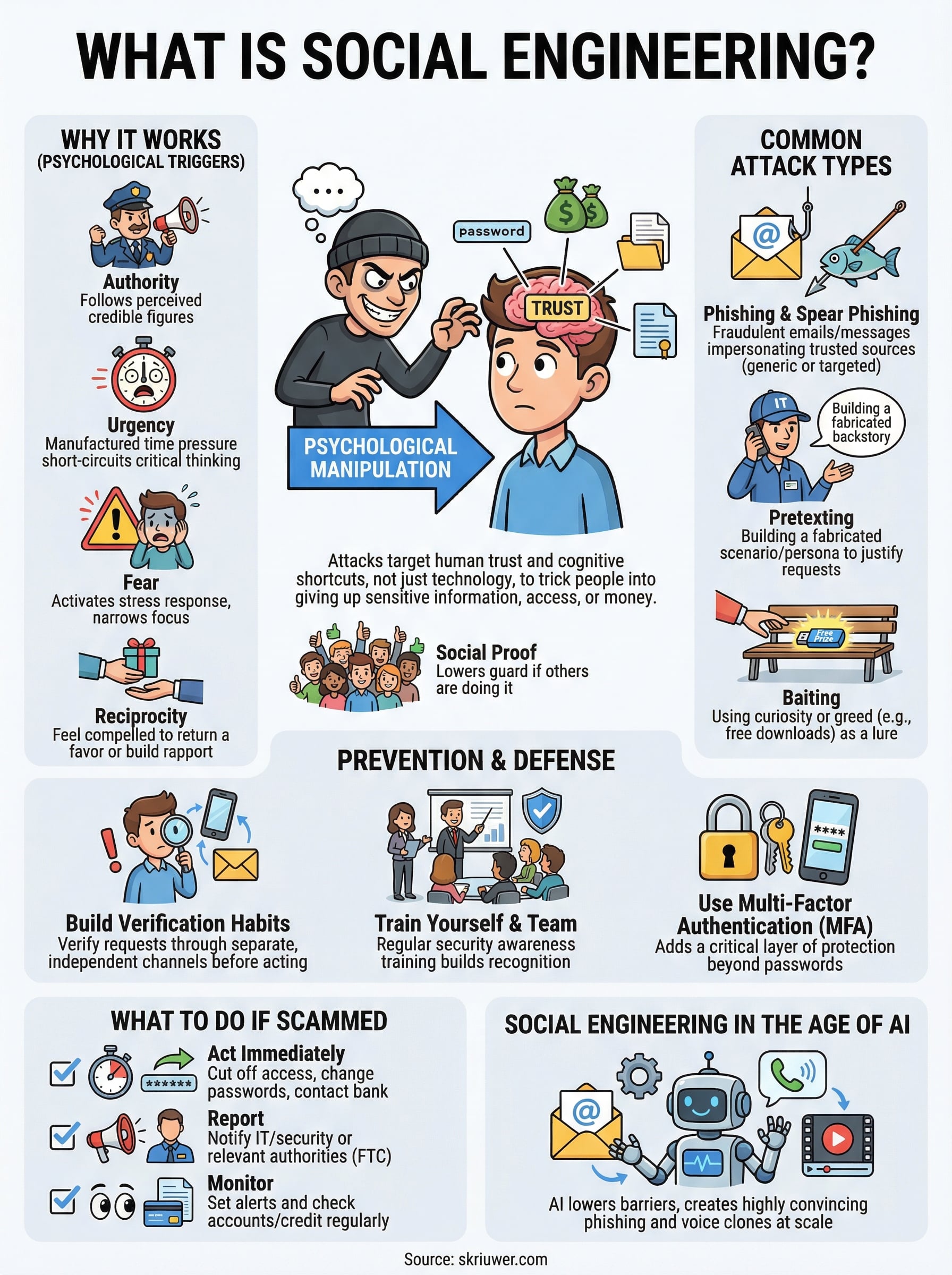
Social engineering is psychological manipulation designed to trick people into giving up sensitive information, access, or money. It targets the human element, which is almost always the weakest link in any security chain. Attackers don't need to break through firewalls when they can simply convince someone to hold the door open.
At Skriuwer, we publish books that expose how manipulation operates across history, politics, and society, from wartime propaganda to modern information control. Social engineering sits squarely in that territory. It uses the same fundamental playbook: exploit trust, manufacture urgency, and bypass critical thinking. Understanding these tactics isn't just useful for protecting your inbox; it builds the kind of skeptical awareness our readers already value.
This article breaks down how social engineering attacks work, walks through real-world examples of the most common techniques, and lays out concrete steps you can take to protect yourself and your organization. Whether you're a complete beginner or just looking to sharpen your defenses, you'll leave with a clear, practical understanding of a threat that costs businesses and individuals billions of dollars every year.
Why social engineering works and why it matters
To understand what is social engineering at a deeper level, you need to look at the psychology it exploits. Attackers don't target your computer. They target your cognitive shortcuts, the mental patterns you rely on to make fast decisions. These shortcuts served humans well for thousands of years, but in a world of instant digital communication, they become vulnerabilities. The moment an attacker understands which emotional levers to pull, technical defenses become almost irrelevant.
What has changed most by 2026 is the tooling. Attackers now use generative AI to write flawless phishing emails in any language, clone a manager's or a relative's voice from a few seconds of audio, and run convincing video deepfakes on live calls. In one widely reported case, a finance worker paid out 25 million dollars after a video call with what turned out to be deepfaked colleagues. The old advice to watch for broken grammar and clumsy wording no longer holds, which makes the habit of pausing to verify a request through a separate, trusted channel more valuable than any spell check.
The psychological triggers attackers exploit
Social engineering works because it taps into predictable human responses. These aren't character flaws. They're universal traits that exist in nearly every person, regardless of education or intelligence.

Here are the core psychological principles attackers use most often:
- Authority: People follow instructions from figures they perceive as credible, whether it's a CEO, a bank, or an IT department. An email that appears to come from your company's director gets acted on immediately.
- Urgency: When someone tells you that your account will be locked in ten minutes, your brain shifts into reaction mode rather than critical thinking mode. Manufactured time pressure short-circuits your ability to pause and verify.
- Fear: A message warning you of a data breach, a legal issue, or a missed payment activates the same stress response as a physical threat. Fear narrows your focus and makes you more likely to comply without questioning.
- Reciprocity: If someone does something for you first, even something small, you feel compelled to return the favor. Attackers use this to build false rapport before making a request.
- Social proof: Seeing that "others have already confirmed their information" or "your colleague has already approved this" lowers your guard because it signals that the action is normal and expected.
The most dangerous social engineering attacks don't feel like attacks at all. They feel like routine interactions.
Why technical defenses aren't enough on their own
Most organizations invest heavily in firewalls, antivirus software, and encryption. These tools are essential, but they protect systems, not people. A well-crafted phishing email that bypasses spam filters and lands in your inbox still requires one human decision to succeed: the click. That's where the real exposure lives.
Research from Verizon's Data Breach Investigations Report has consistently shown that human error is involved in the majority of data breaches. It's not that security tools fail. It's that attackers route around them entirely by targeting the person sitting at the keyboard. No software patch exists for misplaced trust.
Why the stakes are higher than most people think
The financial damage from social engineering runs into the billions annually. But the impact goes beyond money. Compromised credentials can give attackers persistent access to networks for weeks or months before anyone notices. A single employee who responds to a convincing impersonation email can expose an entire organization's customer database, financial records, or internal communications.
For individuals, the consequences are just as serious. Identity theft, drained bank accounts, and fraudulent loans taken out in your name can take years to fully resolve. The damage often extends to your credit history and your ability to access basic financial services.
Understanding why these attacks work gives you a real advantage. Once you recognize the emotional levers being pulled, you can interrupt the automatic response they're designed to trigger. That awareness doesn't require a technical background. It requires knowing what to look for, which is exactly what the rest of this article covers.
Common types of social engineering attacks
Understanding what is social engineering in theory only gets you so far. Real protection comes from recognizing the specific forms these attacks take. Attackers use a range of techniques, each built to exploit a different situation or emotional state. The following are the most common types you're likely to encounter in both personal and professional contexts.
Phishing and spear phishing
Phishing is the most widespread form of social engineering. An attacker sends a fraudulent message, usually by email, that impersonates a trusted source like your bank, your employer, or a government agency. The goal is to get you to click a link, enter your credentials, or download a malicious file before you stop to verify anything.

A spear phishing email that uses your name, your manager's title, and a reference to a project you're actually working on is far harder to dismiss than a generic "click here" message.
Spear phishing is the targeted version. Instead of a generic blast sent to thousands, the attacker researches you specifically and crafts a message that feels personal. This version succeeds at a much higher rate precisely because it doesn't look like an attack at all.
Pretexting
Pretexting involves building a fabricated scenario to justify an unusual request. The attacker invents a plausible role, such as an IT technician, a vendor, or an internal auditor, and uses that persona to get you to hand over information. A caller who knows your company's terminology and job titles can sound completely legitimate.
The key difference between pretexting and phishing is preparation. Pretexting attacks require the attacker to research your organization in advance, learn internal structures, and construct a believable backstory. By the time they reach you, the persona is already well-rehearsed and hard to question.
Baiting
Baiting uses curiosity or greed as the entry point. A classic physical example is leaving a USB drive labeled "Salary Data Q4" in a company parking lot. Someone picks it up, plugs it in, and malware installs automatically. Online baiting works the same way: a free download, a prize notification, or exclusive content lures you into running a malicious file or surrendering your login credentials.
Vishing and smishing
Vishing uses voice calls to manipulate targets, while smishing uses text messages. Both impersonate trusted sources like your bank's fraud team or a delivery service. The attacker creates urgency by claiming there's an unauthorized charge or a package held in customs. Under that manufactured pressure, you provide account numbers, PINs, or one-time verification codes before you've had a chance to confirm who you're actually speaking with.
Real-world social engineering examples
Abstract definitions only go so far. Seeing what is social engineering in documented, real-world cases makes the threat concrete and much easier to recognize. The examples below span different attack types and target profiles, from major corporations to everyday individuals, showing that no one is automatically immune simply because of their role or technical knowledge.
The 2020 Twitter Bitcoin scam
In July 2020, attackers compromised high-profile Twitter accounts belonging to Barack Obama, Elon Musk, Apple, and dozens of others. They didn't break into Twitter's systems through a technical exploit. Instead, they called Twitter employees, impersonated IT staff, and convinced them to hand over access to internal tools. With those tools, the attackers reset account credentials and posted fraudulent Bitcoin solicitations that collected over $100,000 before Twitter could contain the damage.
The most striking detail of this attack is that the employees who complied weren't careless. They were deceived by a convincing, well-researched persona.
This incident demonstrated how a single successful pretexting call can give an attacker control over infrastructure that technical defenses are built to protect. It also showed that even experienced teams inside major technology companies are not inherently safe from manipulation.
The RSA SecurID breach
In 2011, attackers sent targeted spear phishing emails to small groups of RSA employees. The emails carried an Excel attachment titled "2011 Recruitment Plan." At least one employee opened it, which triggered a vulnerability and installed a backdoor. From there, attackers worked their way deeper into RSA's network and stole data related to SecurID authentication tokens, which are used by millions of organizations worldwide for two-factor login.
The breach cost RSA hundreds of millions of dollars and compromised security infrastructure that companies across finance, defense, and government relied on. The entry point was one file opened by one person who had no reason to suspect the email was anything other than routine.
Everyday scams targeting individuals
Large-scale breaches get media coverage, but the majority of social engineering victims are ordinary people. A common scenario involves a phone call from someone claiming to be your bank's fraud department. They reference a real transaction amount to build credibility, then ask you to confirm your PIN or transfer funds to a "secure account." By the time you realize what happened, the money is gone and nearly impossible to trace.
These everyday attacks succeed because they feel completely plausible under pressure, which is exactly what the attacker designs them to do.
How to spot a social engineering attack
Knowing what is social engineering in theory is useful, but the real skill is recognizing an attack while it's happening. That's harder than it sounds because well-crafted attacks are designed to feel completely normal. The warning signs are often subtle, and they're easy to miss when you're distracted, busy, or already emotionally hooked by the scenario the attacker has constructed.
Watch for pressure and urgency
Most social engineering attacks share one core feature: they push you to act fast. Whether it's an email warning you that your account will be suspended in 24 hours or a phone caller insisting they need verification before they can help you, the goal is the same. The attacker wants to stop you from pausing long enough to verify anything.
Any time someone creates artificial pressure around a request for information or access, treat it as a red flag, not a reason to rush.
When you feel that sense of urgency, slow down deliberately. Call the organization directly using a number you find independently, not one provided in the message. Urgency is the attacker's most reliable tool, and resisting it is your most effective counter.
Check the source before you trust it
Spoofed email addresses and fake caller IDs are standard in social engineering attacks. An email might display a legitimate-looking sender name while routing through a completely different domain when you inspect the actual header. A phone call might show your company's main number on your screen while the caller is operating from an entirely separate location.
Before you respond to any unexpected request involving credentials, money, or access, verify the source through a separate channel. If your IT department sends an unusual request, call them directly. If your bank emails you about suspicious activity, log into your account by typing the address yourself rather than clicking any link in the message.
Notice what the request is actually asking for
Legitimate institutions never ask for passwords, PINs, or one-time codes through email or over the phone. If a request involves sharing credentials, transferring funds, or bypassing a standard process for any reason, that's a signal worth stopping at. Attackers rely on the assumption that you'll comply with a reasonable-sounding request without questioning whether the request itself makes sense. If something feels off, verify before you act.
How to prevent social engineering at work and home
Preventing social engineering isn't about installing a single tool or following one rule. Once you understand what is social engineering at its core, you realize that the most effective prevention combines consistent habits, organizational culture, and clear procedures that make manipulation harder to execute at every level.
Build verification habits
Verification is the single most effective behavior you can build against social engineering. Before acting on any unexpected request involving money, credentials, or sensitive data, confirm the request through a separate channel. This means calling a number you find independently, not one included in the message. It also means logging into accounts by typing the address yourself rather than clicking links in emails or texts.

These core habits apply equally at home and at work. Make the following actions routine:
- Never share passwords, PINs, or one-time codes over the phone or through email, regardless of who the requester claims to be.
- Always verify a request for funds or access by contacting the requester through an official, separately sourced contact method.
- Treat unsolicited attachments and links as suspicious by default, even when the sender appears familiar.
- Check email headers when a message asks for anything unusual, since display names can be spoofed while the actual sending domain tells a different story.
Train your team and yourself
At work, regular security awareness training cuts the success rate of social engineering attacks significantly. Training doesn't need to be elaborate. Short, frequent sessions that walk employees through real attack scenarios build recognition faster than annual compliance exercises. Microsoft's Security Awareness Training resources offer accessible guidance for organizations at any scale.
Prevention doesn't require perfection. It requires slowing down long enough to verify before you act.
For home, the same principle applies in a simpler form. Talk with family members about how these attacks work, especially with older relatives and younger children who are statistically more likely to be targeted. The more people around you understand the warning signs, the harder it becomes for an attacker to find a way in through someone you trust.
Multi-factor authentication (MFA) adds a critical layer of protection even when credentials get compromised. Enable it on every account that supports it. Even if an attacker obtains your password through a phishing attempt, MFA blocks the follow-through that turns a stolen credential into a full breach.
What to do if you think you got scammed
Realizing you may have fallen for a social engineering attack is unsettling, but what matters most is how quickly you respond. Understanding what is social engineering makes clear why these attacks are effective: they're built to feel normal until it's too late. Speed matters here. Every minute you wait gives the attacker more time to use whatever they extracted from you.
Act immediately to limit the damage
The first thing you need to do is cut off access. If you shared a password, change it immediately on every account where you use that same credential. If you gave out financial information or authorized a transfer, call your bank directly using the number on the back of your card and report the incident as fraud. Banks have dedicated fraud teams and can sometimes reverse transactions or freeze accounts before money leaves permanently.
Here's a quick checklist of immediate steps:
- Change your passwords on affected accounts and enable multi-factor authentication if it isn't already active.
- Contact your bank or card provider right away if any financial information was shared.
- Disconnect and scan any device where you opened a suspicious file or link, using trusted security software.
- Revoke app permissions or third-party access that was granted during the incident.
Report the incident to the right people
Reporting matters even if you don't expect to recover what was lost. At work, notify your IT or security team immediately so they can assess whether the attacker used your access to move further into the organization. A single compromised account can become a gateway to much larger damage if it goes unreported for even a few hours.
Reporting a scam isn't an admission of failure. It's the action that stops the same attack from reaching someone else.
For personal incidents, you can file a report with the FTC at reportfraud.ftc.gov. If identity theft is involved, the FTC's IdentityTheft.gov walks you through a personalized recovery plan step by step.
Monitor your accounts and credit
After a social engineering incident, set up account alerts on all financial accounts so you receive notifications for every transaction. Check your credit report for new accounts or inquiries you didn't initiate, since attackers sometimes hold stolen information for weeks before using it. Staying on top of your credit activity in the months following an incident is one of the most practical ways to catch secondary damage before it compounds.
Social engineering in the age of AI
AI has changed what is social engineering in a fundamental way. The attacks haven't changed in structure, they still exploit trust, urgency, and authority, but AI has dramatically lowered the barrier to entry for attackers and raised the quality and volume of their output. What once required a skilled writer, hours of research, and careful impersonation can now be generated, personalized, and deployed at scale in minutes.
AI-generated phishing is harder to catch
One of the clearest changes is in the quality of phishing emails. Spelling errors and awkward phrasing used to be reliable signs of a fraudulent message. AI writing tools eliminate those tells almost entirely. Attackers can now feed a target's name, employer, recent activity scraped from LinkedIn, and writing style into a model and receive a highly convincing, personalized message that reads like it was written by someone who actually knows you. The volume and accuracy of these attacks have increased sharply since AI text generation became widely accessible.
Phishing emails that used to be easy to dismiss now require you to look past the words and examine the actual structure of the request.
Your first line of defense can no longer be spotting grammatical mistakes. Your attention needs to shift toward the nature of the request itself and the channel it came through, not just whether the writing looks professional.
Deepfakes and voice cloning
Voice cloning and video deepfakes have introduced a dimension to social engineering that goes far beyond email. Attackers can generate audio that sounds exactly like a known person's voice using a short recording pulled from a public video or podcast. In documented cases, employees have received calls that appeared to come from their CEO or CFO, authorizing urgent wire transfers. Without a verification system in place, those requests are nearly impossible to dispute in the moment.
The practical counter to this threat is the same discipline that protects you against every other form of social engineering: verify through a separate channel before you act. If someone calls you with an unusual request, even if the voice sounds familiar, hang up and call them back using a number you already have on file. AI can clone a voice, but it cannot intercept a call you initiate yourself to a contact you already trust.
Key takeaways
Understanding what is social engineering comes down to one core truth: attackers target people, not systems. Every technique covered in this article, from phishing and pretexting to AI-generated voice clones, relies on exploiting psychological triggers like urgency, authority, and fear. No firewall blocks a well-rehearsed lie delivered to someone under pressure.
Your best defense is a combination of consistent verification habits and the discipline to slow down before you act on any unexpected request. Change passwords immediately if you suspect an incident, report it to your bank or employer without delay, and monitor your accounts in the weeks that follow.
Manipulation doesn't stop at cybersecurity. It runs through history, politics, media, and culture in ways most people never examine closely. If you want to go deeper into how influence and deception have shaped the world, explore the titles available at Skriuwer.
Keep Reading on Skriuwer
Social engineering runs on the same psychology as other forms of influence. These guides go deeper:
- The best books about manipulation, from the classics of influence to guides for spotting it in real life.
- The best dark psychology books on how persuasion and coercion are used to control people.
- Our full curated psychology book collection for understanding how the mind can be exploited and defended.
Books You Might Like

Through the Language Glass
Guy Deutscher

How to Learn Any Language
Barry Farber

